German Federal Printing House, Fraunhofer and Infineon Demonstrate Security of E-Passports for the First Time in the Age of Quantum Computers
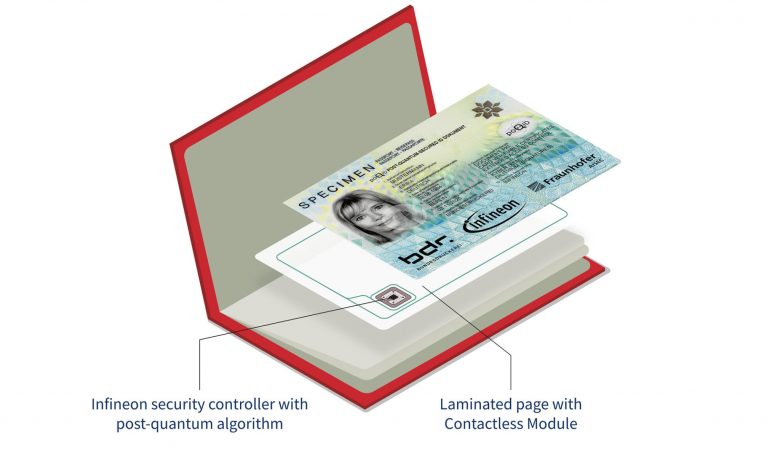
The security controller, created by semiconductor developer Infineon Technologies, protects the biometric and demographic data contained in the electronic passport from classical and quantum computer attacks. ) is the world’s first electronic passport to meet the security requirements of the coming era of quantum computing.
Infineon is a pioneer in the development and implementation of cryptographic mechanisms that can withstand the computing power of quantum computers. By preparing a smooth transition from current security protocols to post-quantum cryptography, Infineon enables the creation of robust and future-proof security solutions.
The technology “uses the Dilithium and Kyber cryptographic methods that the American National Standards Institute NIST selected in July 2022 after a global competition for post-quantum cryptography,” comments Professor Marian Margraf of Fraunhofer AISEC.
“Based on this, we developed protocols for the passport, which were then subjected to further independent security assessments. »
The prototype uses contactless data transfer from an e-passport to a border control terminal, but with a quantum computer-resistant version of the Extended Access Control (EAC) protocol. It also protects the passport holder’s biometric information during authentication.
The updated methods remain compatible with the currently established frameworks. The system was developed as part of a collaborative research project “PoQuID” led by Fraunhofer and funded by the German Federal Ministry for Economic Affairs and Climate Action (BMWK).
prototype post-quantum secure biometric passport from Infineon, Bundesdruckerei and Fraunhofer
Quantum computers are the reality of tomorrow
Due to their processing power, quantum computers have the devastating potential to break the various encryption algorithms currently in use. Quantum computer attacks on modern cryptography are expected to become a reality in the next 10-20 years.
When quantum computers become available, they will be able to perform certain calculations much faster than today’s computers, even threatening common security algorithms such as RSA and ECC. Various Internet standards such as Transport Layer Security (TLS), S/MIME and PGP/GPG use RSA and ECC based cryptography to secure data transmission between smart cards, computers, servers and industrial control systems. Well-known examples are online banking on “https” sites and “instant messaging” encryption on mobile phones.
To solve the problem of mass quantum computing, Infineon is working with its customers, partners and the academic community on all aspects of post-quantum cryptography. As a leading provider of security solutions, Infineon actively researches the efficient implementation of post-quantum cryptography algorithms and promotes future standards that will run efficiently and securely on small devices and embedded devices.
What is a quantum computer?
A quantum computer uses “qubits” that can exist in a so-called superposition. Instead of being either 0 or 1, as is the case with conventional devices, they can be both at the same time. As a result, some calculations can be performed simultaneously and much faster than before, allowing you to solve problems that require processing power that is unattainable for modern systems. By performing operations thousands of times faster, quantum computers open up new possibilities, for example, for searching large databases, simulating chemical and physical reactions, and developing materials.
What is post-quantum cryptography?
Post-quantum cryptography refers to new cryptographic algorithms (usually public key algorithms) that can provide effective protection against attacks using a quantum or conventional computer. Post-quantum cryptography schemes run on conventional computers and do not require a quantum computer to operate. From the user’s point of view, they behave similarly to currently available encryption algorithms (such as RSA or ECC). This makes post-quantum cryptography an ideal replacement providing increased resistance to quantum attacks. To provide protection against the attacks that currently threaten RSA and ECC, post-quantum cryptography schemes rely on new and fundamentally different mathematical foundations. This leads to new problems in the implementation of post-quantum cryptography on small chips with limited memory.